Secure backups are an essential component of every enterprise’s digital security strategy. However, unauthorized third parties can read and alter backups if they aren’t adequately protected. As the use of third-party backup providers becomes more common, this problem is exacerbated.
Using GaraTrust, you can encrypt and cryptographically timestamp your backups to help mitigate these risks. GaraTrust integrates into existing backup processes and can be used with any third-party provider. Anyone can verify that the secure backups have not been altered since the timestamp was created, aiding with potential legal processes. However, only privileged entities with secure decryption keys can restore the backups.

Every enterprise should frequently create backups to ensure a quick recovery in the event of an incident. Of course, the backups must be kept encrypted and secure to remain useful. Two common attacks on backups are unauthorized access and unauthorized modification. Preventing these attacks can go a long way in preventing ransomware attacks but doing so in a large enterprise environment can be challenging.
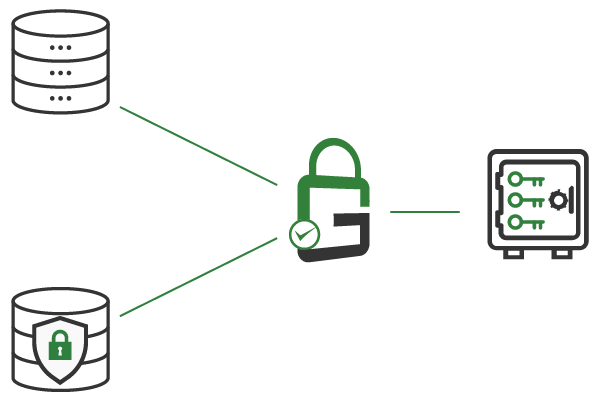
Creating backups at regular intervals is essential, but without proper cybersecurity management, the data can be read by unauthorized entities.
For secure backups to be useful, the enterprise must be able to ensure that the data hasn't been altered since the backup was created.
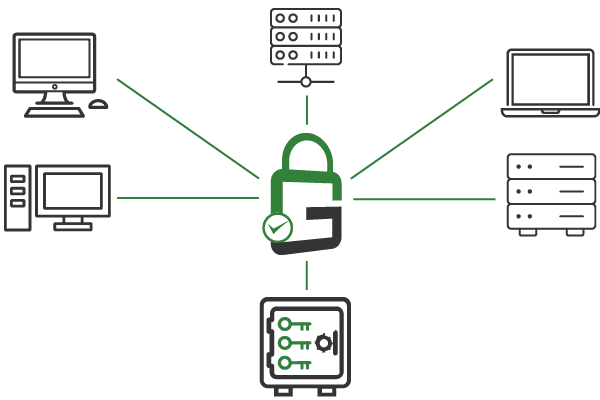
Scaling out data protection to secure all servers and end-user workstations throughout the enterprise is challenging and time-consuming.

With GaraTrust, backups are encrypted to prevent unauthorized users from reading the privileged data, while the decryption keys remain secured in the hardware security module (HSM). GaraTrust is agnostic to which third-party provider is used to perform the backup and transparently integrates into any existing backup processes.
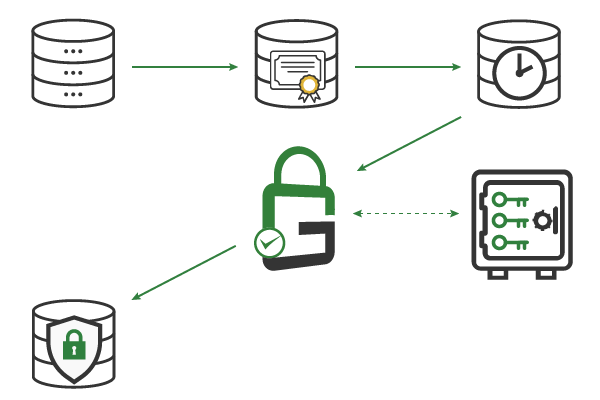
GaraTrust supports cryptographically timestamping backups to ensure that privileged data has not been altered since the backup was created. The enterprise’s signing key signs the backup, and then a cryptographic timestamp is applied by a trusted timestamp authority (TSA). Using a client-side hashing approach, this process is performed exceptionally quickly.
GaraTrust supports transparently encrypting, decrypting, signing, and verifying backup files. This allows GaraTrust to integrate seamlessly into existing backup and restore processes, making deployment easy for organizations of any size.
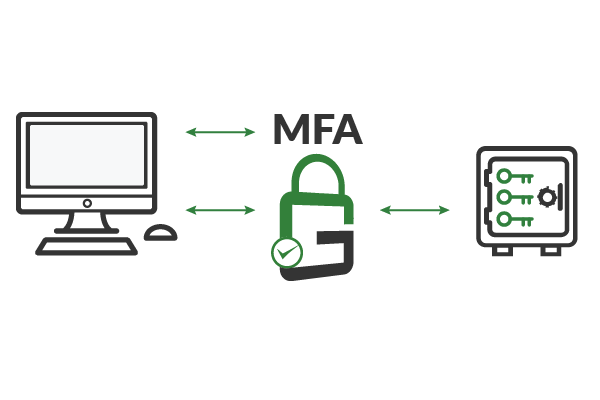
Since backups are created far more often than restore processes occur, GaraTrust’s advanced security controls can be applied to the decryption keys (used during restore) but not to the signing keys (used during backups). multi-factor authentication (MFA), device authentication, approval workflows, IP address whitelisting, notifications, and more.
Schedule a demo to see how GaraTrust can improve the cybersecurity and performance of cryptographic operations throughout your enterprise environment.