Printing documents to sign by hand is tedious, slow, insecure, and environmentally unfriendly. Most businesses would like to take advantage of digital signing but deploying a digital signature solution throughout a large environment is difficult. It’s a struggle to secure a large number of keys while providing access to end-users.
With GaraTrust, all document signing keys are created, stored, and managed centrally within a hardware security module (HSM). End-users are efficiently granted access to the secure signing keys whenever needed, without slowing down the pace of day-to-day business.

While hand-written signatures remain common, they are neither the most secure nor the most efficient way to sign documents.
Digital signatures are far more efficient than written signatures but securely deploying a document signing solution at scale is challenging. It creates an influx of document signing keys & certificates to manage and may require building integrations from end-user software to key managers or hardware security modules (HSMs).
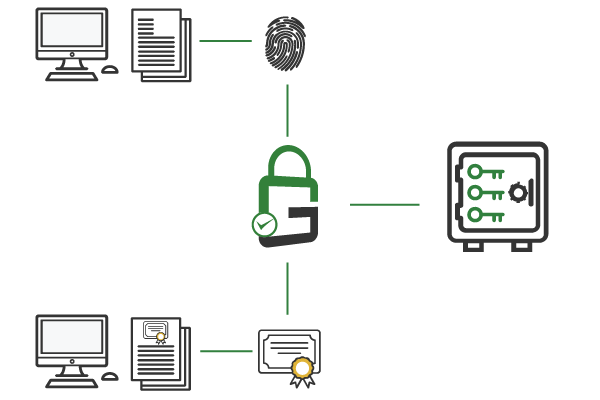
Properly protecting document signing keys and enforcing granular security controls, such as multi-factor authentication (MFA), is critical yet challenging.
Users are accustomed to sub-second file processing. Security controls cannot inhibit this level of performance.
To reduce training requirements, a document signing solution must integrate with existing enterprise software and tools.

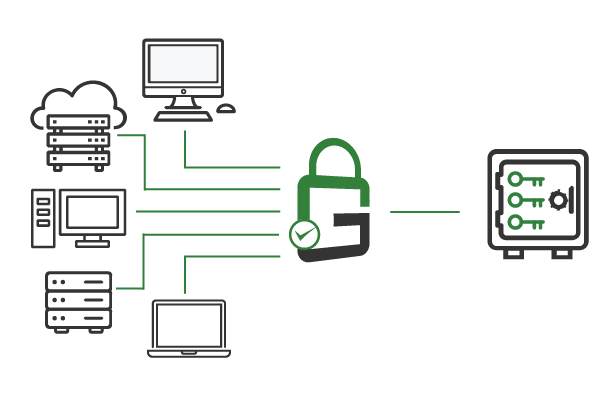
GaraTrust is deployed on customer-managed infrastructure between the HSM and the document signing clients, restricting those document signing clients to proxied key access.
The result is that all document signing keys remain secured and non-exportable in the HSM at all times, while end-users can still use the keys they need to efficiently sign documents. GaraTrust further secures keys via granular access controls and features, such as multi-factor authentication (MFA), device authentication, and more.
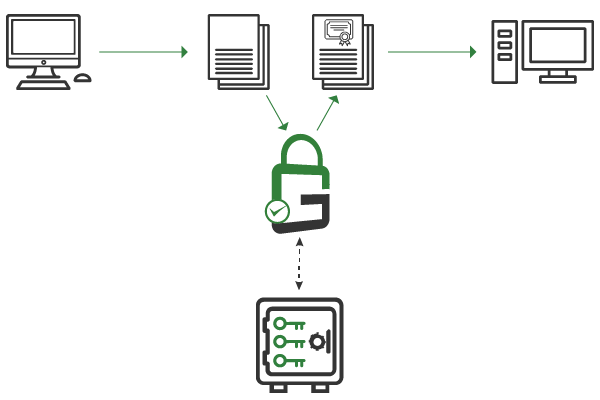
GaraTrust uses a digital hash signing architecture: signing clients hash the document they need to sign before sending it over the network to create the signature.
This technique limits the amount of data being transmitted over the network, so documents are signed quickly while the document signing keys remain secured in the hardware security module (HSM).
GaraTrust supports all the privileged access management signing tools needed to enable document signing throughout any environment, from native client integration into PDF and Microsoft Office clients to bulk document signing utilities that can be easily automated and deployed at scale.
GaraTrust supports signing many types of documents including PDFs, Microsoft Office documents, XML files, and unstructured documents via cryptographic message syntax (CMS).
Yes, GaraTrust supports document signing solutions for many common PDF tools.
Yes, GaraTrust supports bulk document signing via a command-line document signing tool that can process large numbers of documents in a directory.
Yes, GaraTrust has open APIs and pre-built SDKs that developers can use to embed document signing functionality into their applications.
For manual document signing solutions, GaraTrust supports multi-factor authentication (MFA), approval workflows, just-in-time access, device authentication, IP address whitelisting, audit notifications, and granular key permissions.
For automated document signing, GaraTrust supports device authentication, IP address whitelisting, audit notifications, and granular key permissions.
GaraTrust supports a quorum-based approval process where a quorum of approvers must approve the document signing request before the signature is generated. If any approver rejects the request, the signature is not generated. GaraTrust even supports tiers of quorums with each tier having its own quorum size. For example, you could configure it so that at least three contracts personnel must approve the document signing request. Once that is complete, at least one C-level personnel must approve it. And so on as you see fit.
Schedule a demo to see how GaraTrust can improve the security and performance of cryptographic operations throughout your environment.