Ransomware attacks have become alarmingly common, and, unfortunately, experts predict that they will only become more frequent and more severe in the coming years.
GaraSign provides cybersecurity protection against ransomware with a variety of security controls, including restricted access to sensitive data and decryption keys, granular access controls like multi-factor authentication (MFA) and device authentication, and support for digitally signing and timestamping backups.

It is best practice to cryptographically timestamp your data before you encrypt it. This allows you to quickly identify if the data has been tampered with at any point in time. GaraSign integrates with all major, trusted timestamp authorities (TSA) to support cryptographic timestamping seamlessly.
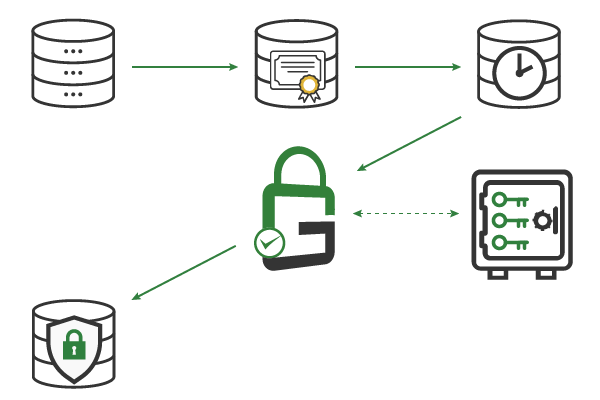
Whenever possible, encrypt data at rest using a self-managed (i.e., on-premise) Key Management Service (KMS). This is especially important when the third-party is the one storing the data, as is the case with cloud providers. By encrypting the data before it is sent to the storage provider, you benefit from the storage provider’s scale without sacrificing the confidentiality or integrity of your own data.
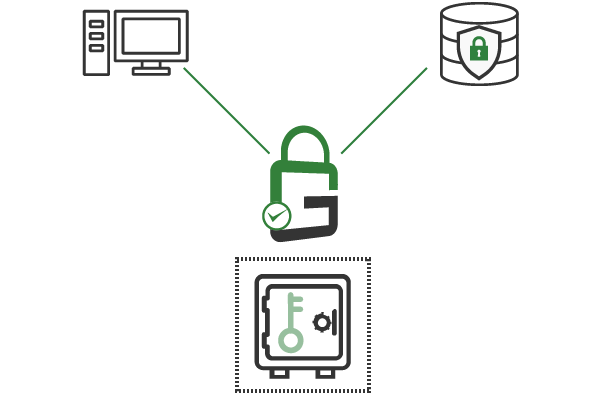
By default, keep the private keys for decryption disabled. Since they are only needed when restoring backups and are therefore not needed frequently, you should only enable them when necessary and immediately disable them again after they are used. With GaraSign, any cryptographic key can be disabled with a few clicks from the GaraSign interface.
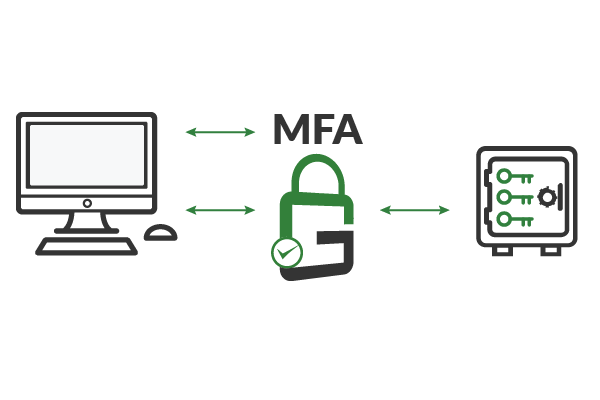
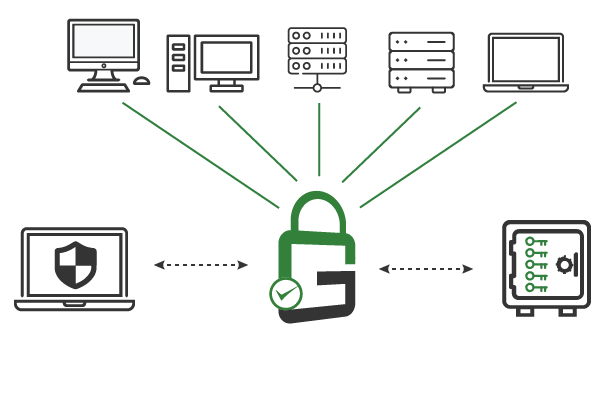
Ensure that only authorized and authenticated end-users can use the decryption keys needed to access backups. GaraSign supports granular access controls, such as multi-factor authentication (MFA), device authentication, and approval workflows, on a per-key or per-user basis.
With GaraSign, all backups are digitally signed, cryptographically timestamped, and encrypted while the decryption keys remain secured in a certified hardware security module (HSM). Security policy can be established on a per-key or per-user basis from a single interface, and any cryptographic key can be disabled with a few clicks. Granular cybersecurity controls, such as multi-factor authentication (MFA), device authentication, approval workflows, and more, ensure that only authorized and authenticated end-users can access decryption keys and, thus, the encrypted data.
Cryptographically timestamp backups and other databases to ensure the integrity of the data and to meet legal requirements.
Attach a digital signature to all backups and other databases in order to prevent third-parties from tampering with the data.
Encrypt all backups and store the decryption keys in a non-exportable state in a certified hardware security module (HSM).
Leave decryption keys disabled until seconds before an authorized and authenticated end-user needs access.
Enforce granular access on decryption keys, including multi-factor authentication (MFA), device authentication, approval workflows, notifications, and more.
Audits can easily be performed at any time. Compliance with data security regulations is drastically simplified.
Schedule a demo to see how GaraSign can improve the cybersecurity and performance of cryptographic operations throughout your environment.
321 Tenth Ave #1208
San Diego, CA 92101
(858) 751-4865
info@garantir.io
Copyright © 2023 Garantir LLC. All Rights Reserved.