
The ramifications of an improperly implemented cryptographic architecture can be catastrophic. While modern cryptographic algorithms are extremely secure, even a minor implementation error can cause major vulnerabilities. Garantir can help your enterprise ensure a seamless and secure deployment.
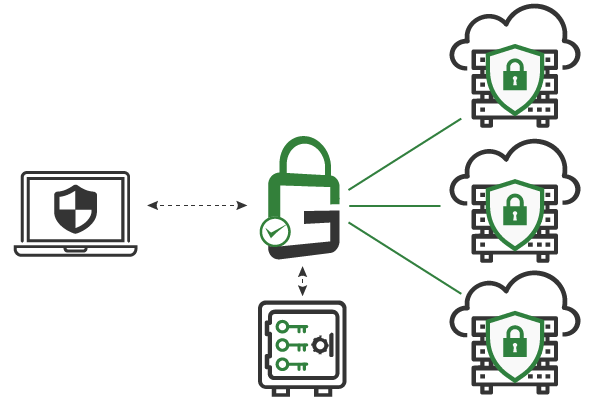
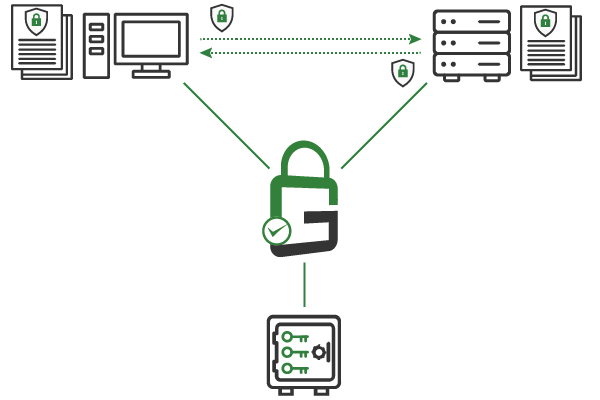
With a variety of different systems, platforms, and software in use, enterprises require cryptographic architectures that provide seamless interoperability. Garantir has the expertise to architect cryptographic systems that can be deployed in any environment.
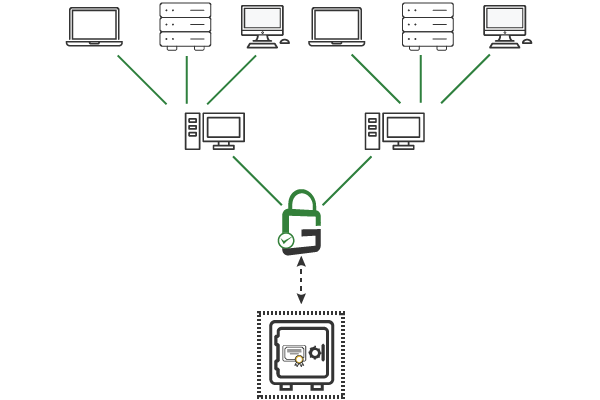
Two essential components of a secure cryptographic architecture are PKI and key management. The PKI root of trust and all of the cryptographic keys must be properly protected. At the same time, security leaders must be able to centrally grant, revoke, manage, audit all access to and usage of the keys. The Garantir team is experienced in deploying systems of this design.
Schedule a free consultation to see how the Garantir team can help improve your enterprise's security posture.