Keeping data secure is a top priority for cybersecurity leaders across dozens of verticals.
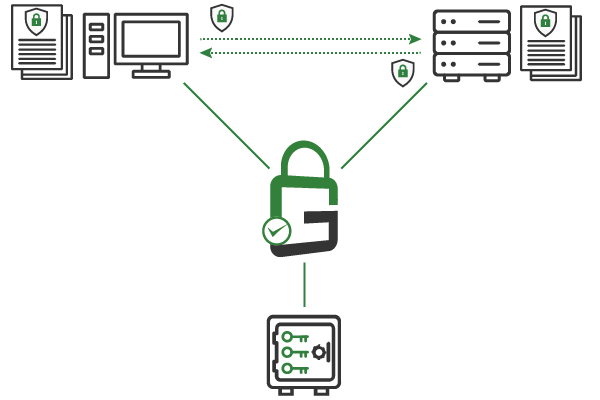
With GaraSign, all data in transit and at rest is encrypted, decryption keys are always protected and centrally managed, and the enterprise can easily enforce granular access controls on the decryption keys.
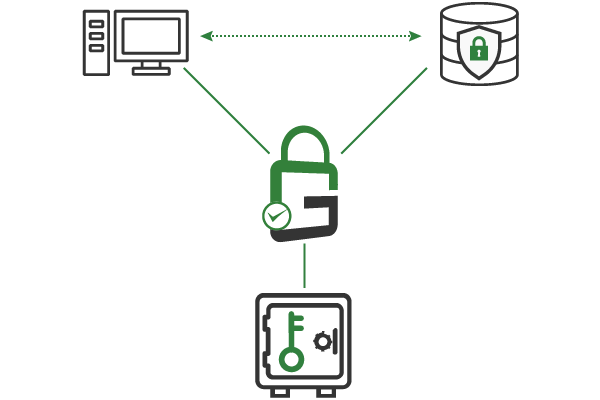
Secure network traffic and other data in transit with protocols like transport layer security (TLS) and secure shell (SSH). This encrypts all data transmitted over the enterprise network, preventing unauthorized third parties from accessing and viewing sensitive data. GaraSign is compatible with all public-private key use cases, including TLS, SSH, remote desktop protocol (RDP), virtual private network (VPN), and much more.
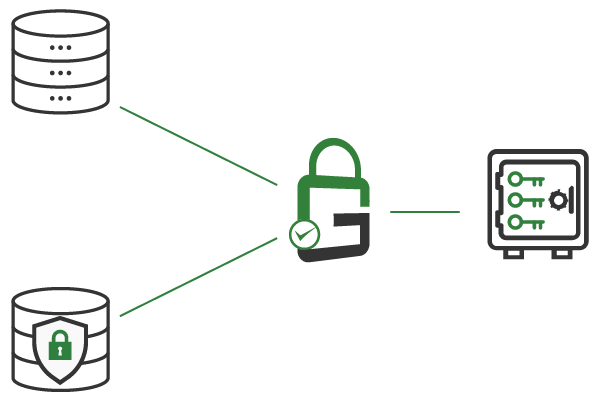
Use strong encryption to ensure that only authorized and authenticated end-users can view databases and backups. This protects enterprise data, intellectual property, confidential strategic plans, and other sensitive information. It also helps the enterprise to comply with data security regulations. GaraSign supports all major encryption algorithms.
Strong encryption is only effective when the decryption keys are properly protected. If attackers gain access to your decryption keys, even the strongest encryption algorithms are rendered useless. That’s why it’s essential to store decryption keys in a non-exportable state in a certified hardware security module (HSM).
Ensure that only authorized and authenticated end-users can use the decryption keys needed to access encrypted databases and backups. GaraSign supports granular access controls, such as multi-factor authentication (MFA), device authentication, and approval workflows, on a per-key or per-user basis.
With GaraSign, all data is encrypted, and the decryption keys are always secured in a centrally managed hardware security module (HSM). Authorized end-users can use the keys as needed by authenticating to GaraSign, which then performs the private key operation on the client’s behalf. GaraSign allows customers to enforce granular controls, like multi-factor authentication (MFA) and device authentication, on a per-key or per-user basis with a few clicks from a single admin interface.
Encrypt all data in transit with protocols like transport layer security (TLS) and secure shell (SSH), and encrypt all data at rest with transparent data encryption (TDE).
Generate and store all decryption keys in a non-exportable state in certified hardware security module (HSM) or key manager.
Enforce granular access on decryption keys, including multi-factor authentication (MFA), device authentication, approval workflows, notifications, and more.
Decryption keys are stored in a centrally managed hardware security module (HSM), and key policies are set from a single interface.
Leave decryption keys disabled until seconds before an authorized and authenticated end-user needs access.
Audits can be conducted at any time and compliance with data security regulations is easily achieved,
Schedule a demo to see how GaraSign can improve the cybersecurity and performance of cryptographic operations throughout your environment.
321 Tenth Ave #1208
San Diego, CA 92101
(858) 751-4865
info@garantir.io
Copyright © 2023 Garantir LLC. All Rights Reserved.